AI Assistants
AI Assistants are the AI-powered agents that interact with users in Workspace Chat. Each assistant can answer questions, suggest diagnostic tasks, run automation, and recommend next steps — all within the permissions of the workspace and the user.
How Assistants Work
When you ask a question in Workspace Chat, the selected assistant:
- Reviews existing production insights — structured results from background tasks that have already run
- Identifies relevant issues that have already been flagged
- Suggests and runs additional diagnostic tasks targeted at your question
- Combines all of this context to produce an actionable answer
Assistants are not a single generic AI. Each workspace can have multiple assistants, each configured with a different personality, permission level, and autonomy threshold.
Built-In Assistant Profiles
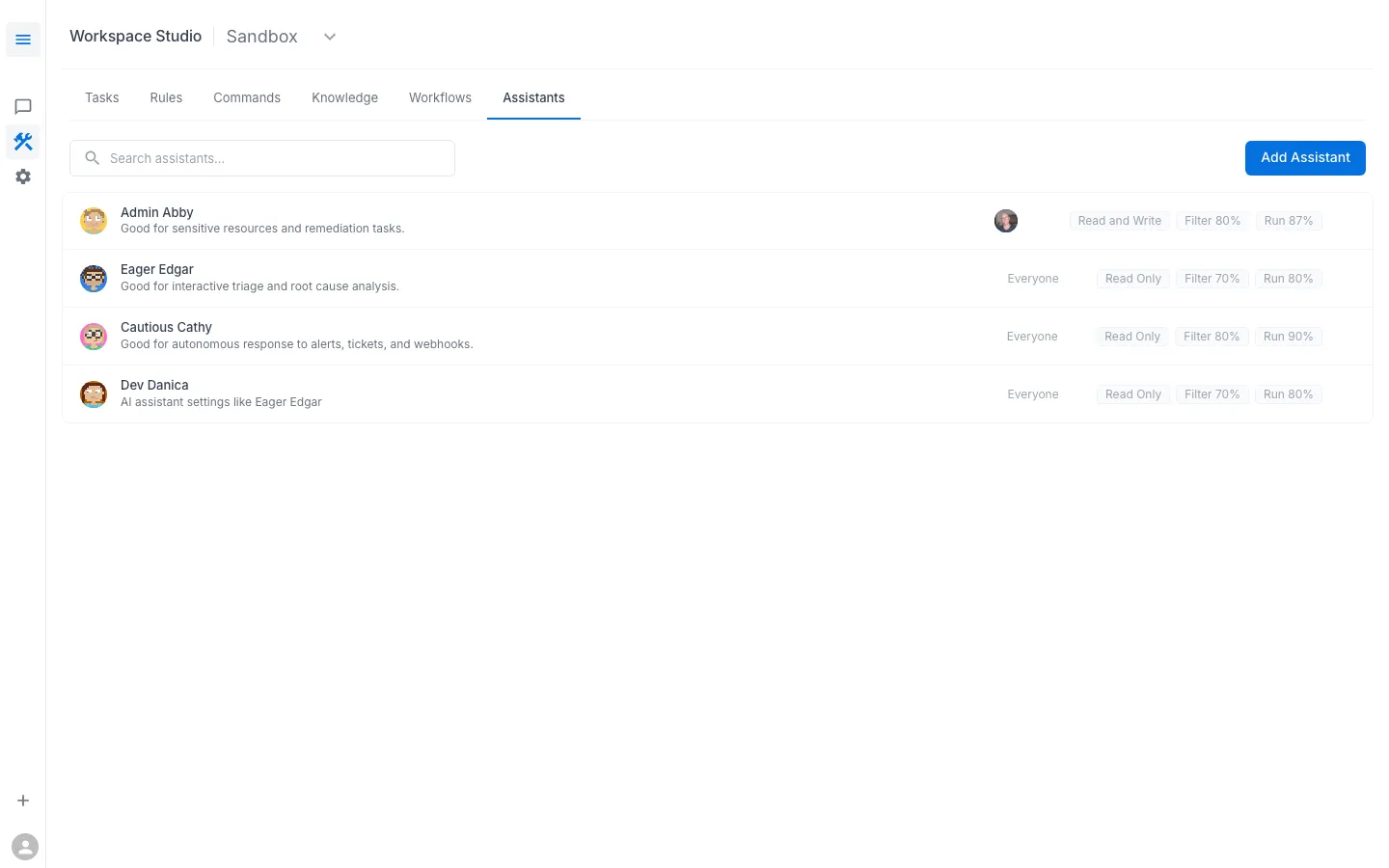
RunWhen ships with several assistant profiles out of the box. Each has different defaults for how aggressively it filters results and how willing it is to run tasks autonomously:
| Assistant | Description | Access | Run Threshold |
|---|---|---|---|
| Admin Abby | Full access for sensitive resources and remediation tasks | Read & Write | 87% |
| Eager Edgar | Good for interactive triage and root cause analysis — readily runs diagnostics | Read Only | 80% |
| Cautious Cathy | Good for autonomous response to alerts, tickets, and webhooks — higher filter threshold reduces noise | Read Only | 90% |
| Dev Danica | Developer-friendly assistant for everyday troubleshooting | Read Only | 80% |
You can create custom assistants from Workspace Studio > Assistants > Add Assistant.
Rules: Shaping Assistant Behavior
Rules are instructions that tell assistants how to interpret and respond to specific situations. They let you tune assistant behavior without changing code.
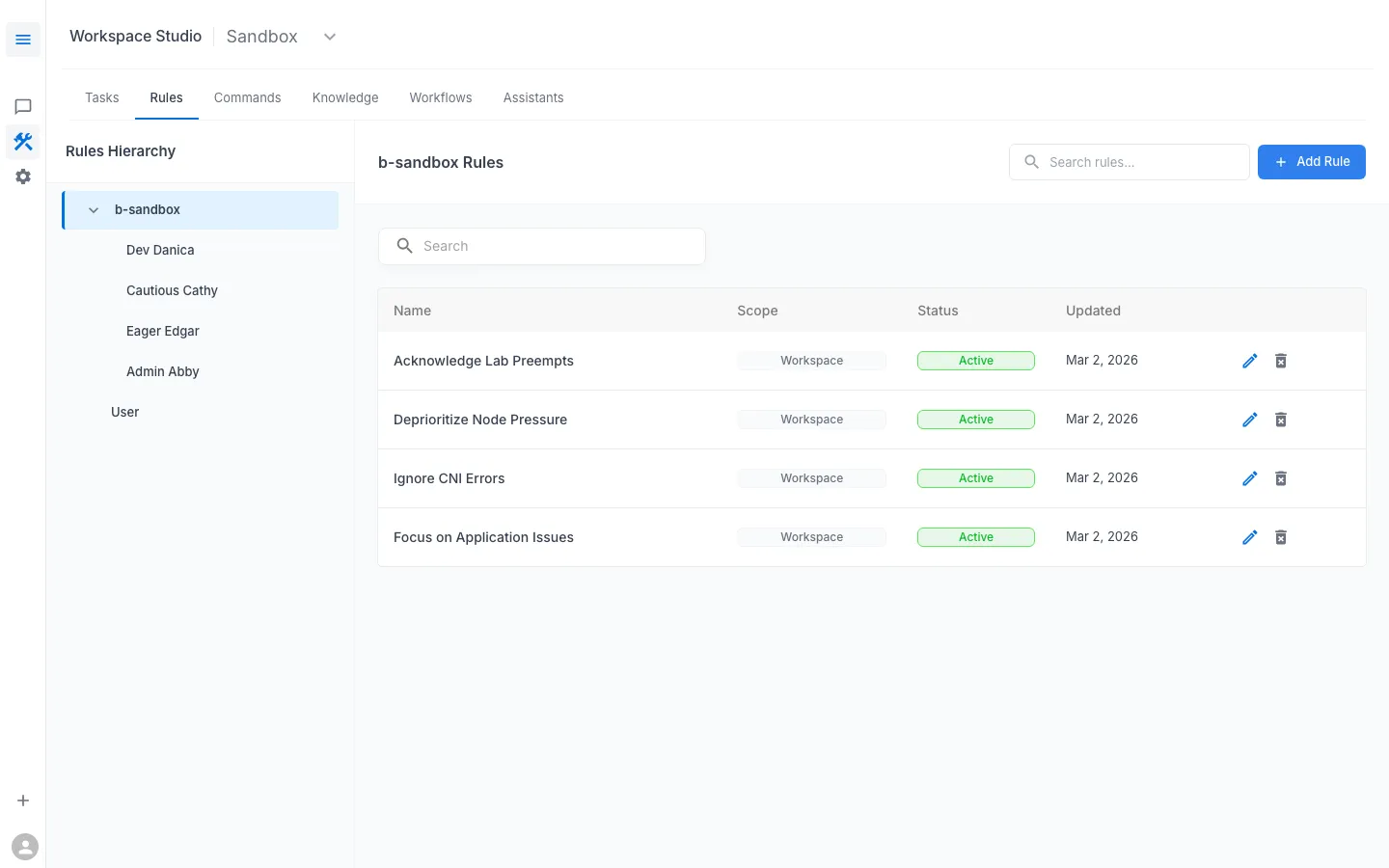
Common uses for rules:
- De-noise the environment — e.g., “Acknowledge Lab Preempts” tells assistants that spot-instance preemptions are expected in this cluster and not actionable
- Prioritize what matters — e.g., “Focus on Application Issues” tells the assistant to emphasize app-layer problems over infrastructure noise
- Deprioritize known constraints — e.g., “Deprioritize Node Pressure” prevents the assistant from flagging expected resource pressure in a lab environment
Rules can be scoped to the entire workspace or to a specific assistant. They are managed under Workspace Studio > Rules.
Commands: Reusable Multi-Step Procedures
Commands are named procedures that an assistant can execute when invoked by a user (or triggered by an event). They bundle together a sequence of tasks and instructions into a single action.
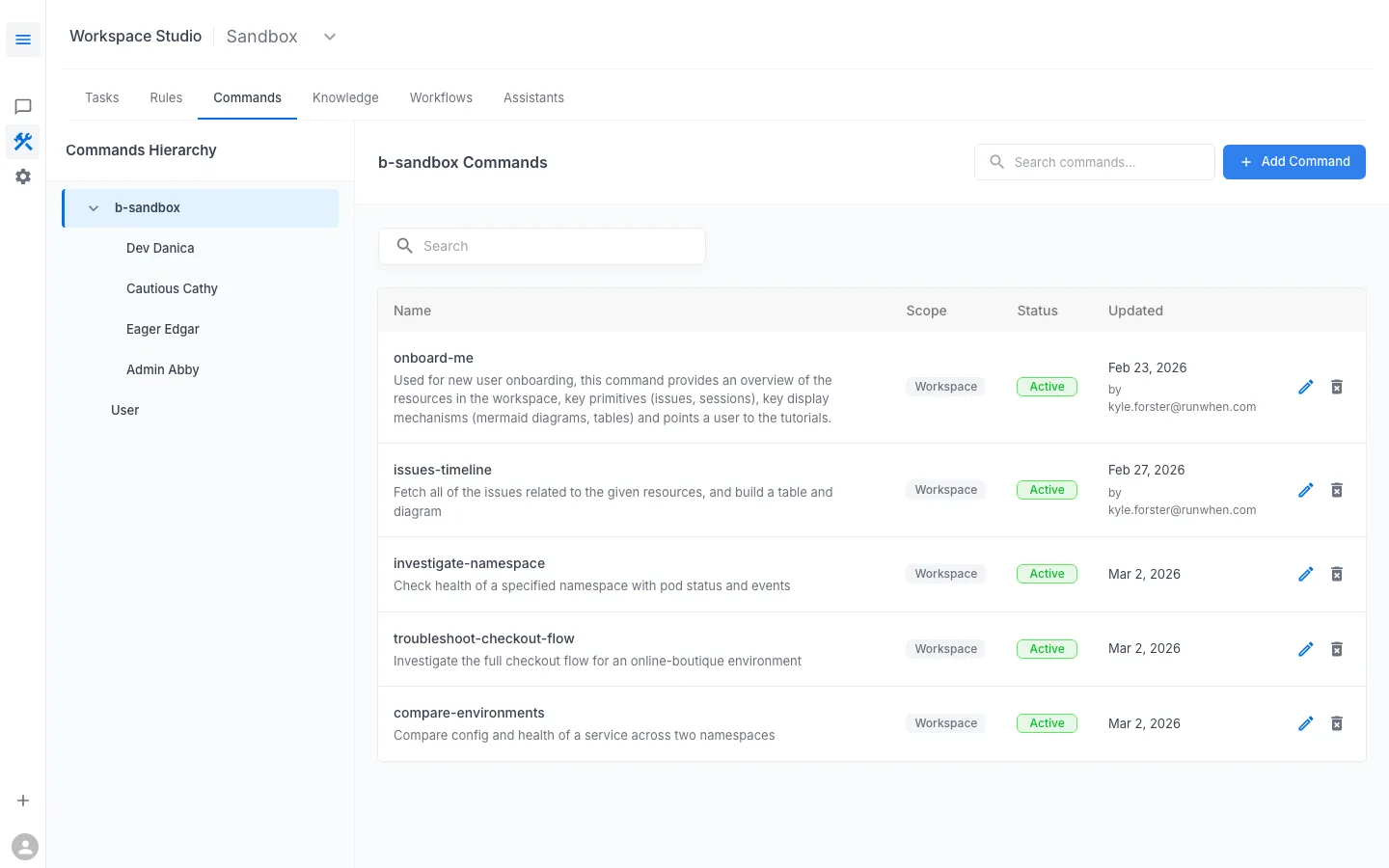
Examples of commands:
onboard-me— walks a new user through the workspace, showing key resources and how to get startedinvestigate-namespace— checks health of a Kubernetes namespace including pod status and recent eventstroubleshoot-checkout-flow— runs the full diagnostic sequence for the checkout servicecompare-environments— compares config and health of a service across two namespaces (e.g., dev vs. prod)
Commands are managed under Workspace Studio > Commands.
Permissions and RBAC
AI Assistants have their own RBAC model that controls what they are allowed to do. This operates at two levels:
1. Assistant-Level Permissions
Each assistant is configured with its own access controls:
- Access level — Read Only or Read and Write, determining whether the assistant can run remediation tasks or only diagnostic ones
- Task tag filters — assistants can be scoped to only run tasks matching specific tags, restricting which categories of automation they have access to
- Filter and Run thresholds — control how aggressively the assistant filters results and how willing it is to run tasks autonomously
2. User and Group Assignment
Users (or groups) are assigned to specific assistants. This means:
- Different team members can be given access to different assistants with different capability levels
- A developer might use Dev Danica (read-only, lower thresholds), while an SRE uses Admin Abby (read-write, broader task access)
- Group assignments let you manage assistant access at the team level rather than per-user
Workspace Isolation
Regardless of assistant configuration:
- Assistants cannot cross workspace boundaries or reference resources from other workspaces
- Assistants cannot retrieve secret values — they can use tasks that rely on secrets, but only through the secure execution pipeline
- All AI-triggered actions are auditable
